 April 11, 2026
April 11, 2026
How Secure is Cheap RDP and What Protection Does Buy RDP Offer?
Summary
Article Name
How Secure is Cheap RDP and What Protection Does Buy RDP Offer?
Description
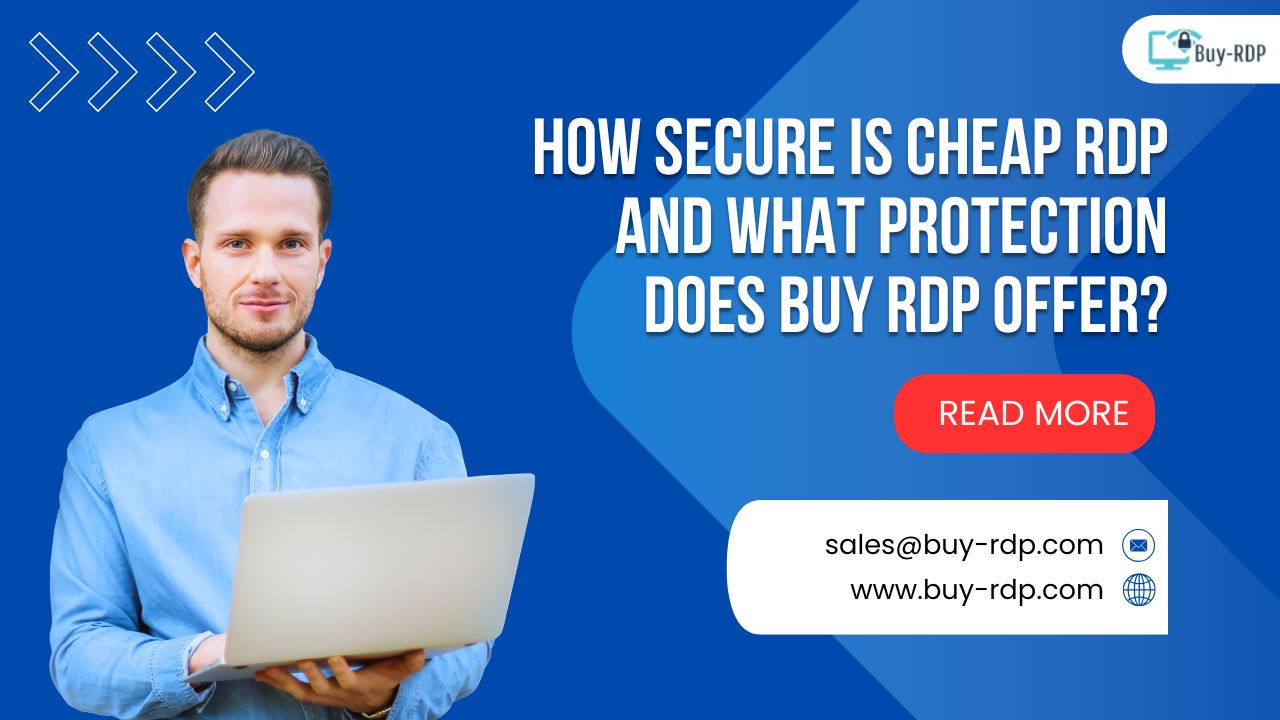
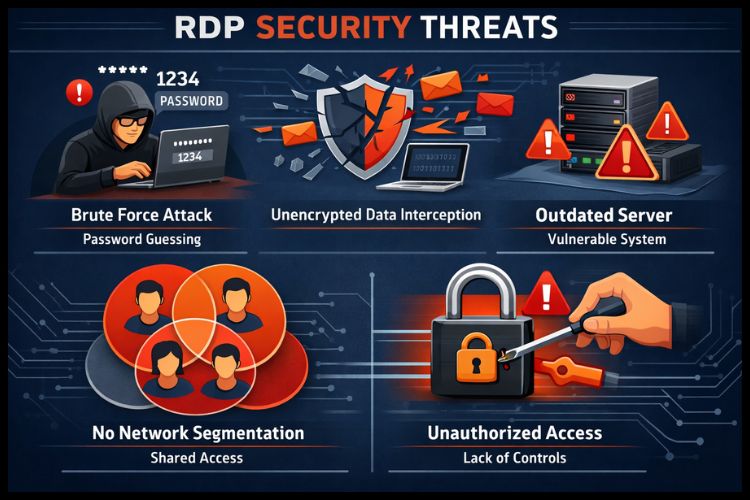
Let's explore the security landscape of RDP services and examine what genuine protection looks like.
Author
Dikshita
Publisher Name
Buy RDP
Publisher Logo


Leave a comment